Have you ever wondered how many details are silently revealed every time you visit a website? As someone who often needs to check my own IP address or verify connection details, I grew increasingly tired of intrusive advertisements and complicated designs found on many common IP checking sites. Driven by frustration, I created my own elegant and entirely ad-free IP checker, IP Beacon. Feel free to try it yourself at https://my.0at.de/. If you like what you see, I am delighted to offer the complete script as a ZIP download so you can easily deploy it on your own server.
LONDON’S iCloud BREACH: THE DAY PRIVACY DIED AND DIGITAL SECURITY FAILED – There was a day not very long ago when our private communications, personal photos, financial data and intimate notes were something sacred and untouchable. We trusted tech giants like Apple with the implicit certainty that the cloud platforms they provided were secure and beyond the invasive reach of any external eyes, private or governmental. However, on a seemingly unremarkable afternoon in London, the entire foundation upon which we had built this digital trust collapsed irreparably. Suddenly, the abstract dangers of digital privacy breaches became painfully concrete.
Two-factor authentication (2FA) emerges as a bulwark in the digital age, an indispensable safeguard against the ever-present threats posed by cybercriminals. Beyond the classic username password combination, 2FA adds an extra layer that repels even the most sophisticated attacks. For a forensic expert like me, implementing 2FA is not just a recommendation; it is an absolute necessity. In the following narrative I will not only shed light on the critical risks of foregoing 2FA but also share my personal journey in the digital underground, a world where bits and bytes form the very fabric of existence.
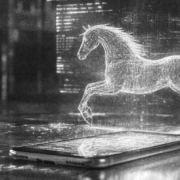
China’s latest AI sensation, DeepSeek, has taken the tech world by storm, and not just for its impressive capabilities. In record time, this startup has climbed the app charts, putting pressure on established players like OpenAI. What makes DeepSeek stand out is its claim of delivering performance comparable to Western AI models while requiring significantly fewer resources. Sounds too good to be true? Perhaps, because a massive security flaw has already exposed serious weaknesses in how DeepSeek handles data privacy.
Pegasus: An invisible threat to our privacy – Pegasus is an advanced Trojan software used by governments to gain access to the data of target individuals. Developed by the Israeli NSO Group, it is often used as a tool to combat terrorism and serious crime. However, it poses a tremendous threat to privacy as it is capable of infiltrating smartphones and accessing all data unnoticed. Once Pegasus infects a device, secure communication is no longer possible – even on supposedly secure platforms like Telegram. The spyware can intercept messages before they are encrypted or after they are decrypted.
The rapid advancement of artificial intelligence has already revolutionized many aspects of life, but it has also exposed a dark side that demands urgent attention: the creation and distribution of AI-generated child abuse imagery. This emerging form of crime poses a significant threat, challenging law enforcement agencies while raising fundamental ethical and societal concerns.
The Bavarian police have added a new, powerful tool to their arsenal: Palantir software. Known from the Batman universe, Gotham – the technology behind Palantir – analyzes unfathomable amounts of data and discovers connections that would be invisible to the human eye. However, with the deployment of this technology in Bavaria, the question arises whether we are on the path to a transparent society.
Imagine, I recently faced the challenge of sending all my passwords as part of my digital legacy. Being a technology and security aficionado, I was well aware that conventional messenger services hardly provide the necessary level of security anymore. So I thought to myself: “Why not encrypt the text before sending and protect my sensitive data from the prying eyes of unauthorized individuals?”
Photos and videos are essential components of our modern society and serve as indispensable evidence in law enforcement, journalism, and science. However, the authenticity of these media is increasingly questioned due to manipulations and forgeries. One key technology to verify the genuineness of visual material is the analysis of shadows, a fascinating process that often unfolds like a gripping crime thriller. This technique examines the light sources and their interaction with the objects in the image to identify anomalies that could indicate manipulations.
Stay one step ahead of your competition and let us document competitive, trademark-related or similar infringements, insults or online bullying as compelling evidence.